What’s more, Google penalizes WordPress sites when they’re infected with malware because it deems them unsafe or risky to visit and can issue owners with a Google review ban.
This is why it pays to get your site checked out immediately and have your infected files removed as soon as possible. Your SEO results (and your revenue) depend on it!
Then, you’ll want to install website security measures so malware attacks don’t happen again.
But we’re getting ahead of ourselves; first, keep reading to learn how to clean up your site with our fast and easy WordPress malware removal tips.
And stick around until the end if you’d like to learn about the symptoms of malware and how sites get infected!
How To Remove Malware From a WordPress Site
If you notice any suspicious signs, it’s time to get started.
We suggest you tackle malware removal in WordPress in one of three ways:
1. Remove it manually
2. Use a plugin to remove it and clean your site
3. Reach out to an expert and ask for help
Before trying these options, immediately back up your site with a WordPress backup plugin or through your hosting provider. While you’re at it, switch on automated website backups so you always have a save point.
And, familiarize yourself with an FTP (File Transfer Protocol) client. These programs, such as FileZilla, help you make manual edits to WordPress.
How to remove WordPress malware: A quick summary
Malware might prevent you from taking action for some of the options below. When that’s the case, speak to an expert immediately.
| Step | In brief |
| Remove malware manually from your website | |
| 1. Put your site into maintenance mode | Use a plugin to show visitors you’re working behind the scenes |
| 2. Scan your computer | Run a malware scan to check your device isn’t infected |
| 3. Back up your WordPress core files and database | Back up your important files if you know they’re safe, or check if you have a recent backup before the infection |
| 4. Download and examine backup files | Check you have all the core files WordPress needs backed up and safe |
| 5. Delete all files in the public_html folder | Erase existing files to purge the malware manually |
| 6. Reinstall WordPress and reset database credentials | Redownload WordPress and upload it via FTP, then check your database details match in wp-config and your server |
| 7. Reset permalinks | Head to WordPress’s Settings tab, then Permalinks, then save changes to reset your site’s links |
| 8. Reinstall plugins and themes | Head back to the plugin and theme libraries to reinstall only the software you need |
| 9. Reupload your images | Refer to the images you downloaded in the backup and either reupload them or find better-quality alternatives |
| 10. Install and run security plugins | Choose a plugin such as Sucuri or Jetpack to secure your site and scan for malware |
| Remove malware with a WordPress plugin | |
| 1. Scan WordPress for malware | Use a security plugin to scan for malware and isolate it using the software |
| 2. Remove malware from your WordPress site | Where possible, use the plugin to review and remove any malware found |
| 3. Remove malware warnings from Google | Contact Google via Search Console (through Security Issues) and request a review of your site’s safety |
| Ask an expert to remove malware from your site | |
How to remove malware from your website manually: A 10-step process
When you remove malware manually from your infected WordPress site, you ensure there’s no trace of malicious code or programming left. It’s complex but thorough!
The following manual steps help you perform a “malware cleanup” of your website’s files inside and out, which effectively means deleting WordPress and performing a WordPress installation from scratch.
If, however, you’d prefer to let a plugin do the hard work for you, skip ahead. Or, if you’re really unsure how to proceed, call in an expert!
Step 1: Put your site into maintenance mode
Maintenance mode tells your visitors that your site is down temporarily while you’re fixing a problem.
We recommend using a plugin to activate maintenance mode before you start cleaning malicious software manually.
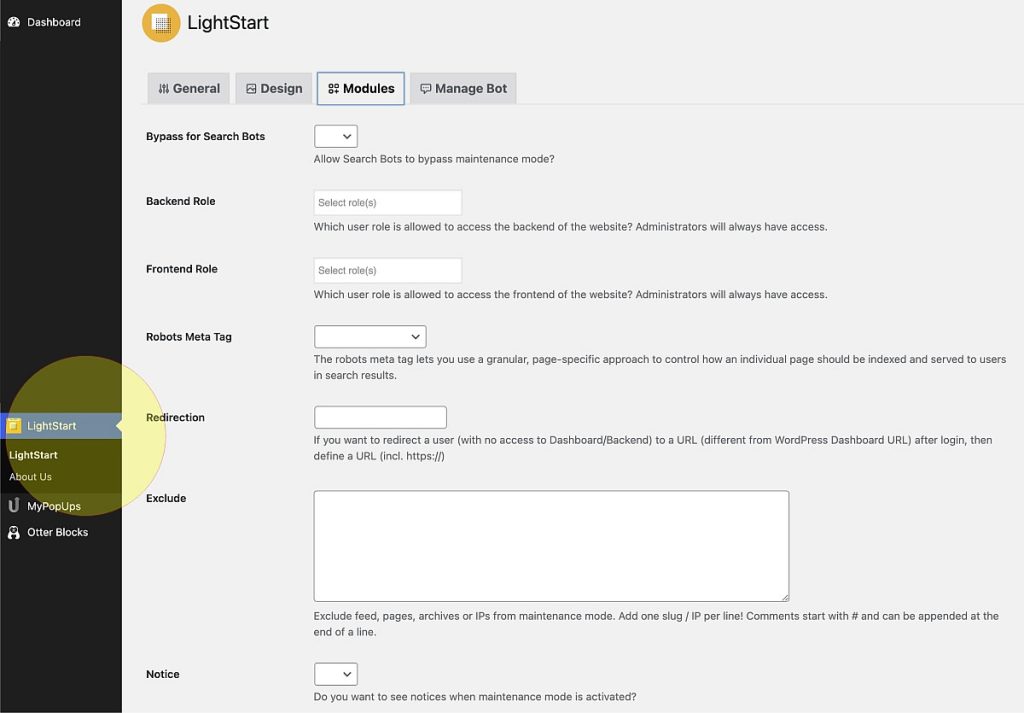
Download and activate the Lightstart plugin and access it from WordPress’s left sidebar.
Tick the “Activated” box. This should now show a maintenance message when people access your site.
Remember to tick “Deactivated” once you clean up the malware, or your visitors may think there’s still a problem.
Step 2: Scan your computer
Naturally, the last thing you want is to move WordPress malware over to your computer.
So, regardless of your hardware and operating system, run a full system scan for malware and viruses if you haven’t done so already.
Step 3: Back up your WordPress core files and database
As we said before these steps, we recommend you back up your core files and database during malware removal. Doing so ensures you don’t accidentally delete or alter any crucial files.
That said, there’s a chance malware might have corrupted your core files, which means backing them up could prolong the problem.
If you really can’t be sure they’re safe to back up, call in an expert for help.
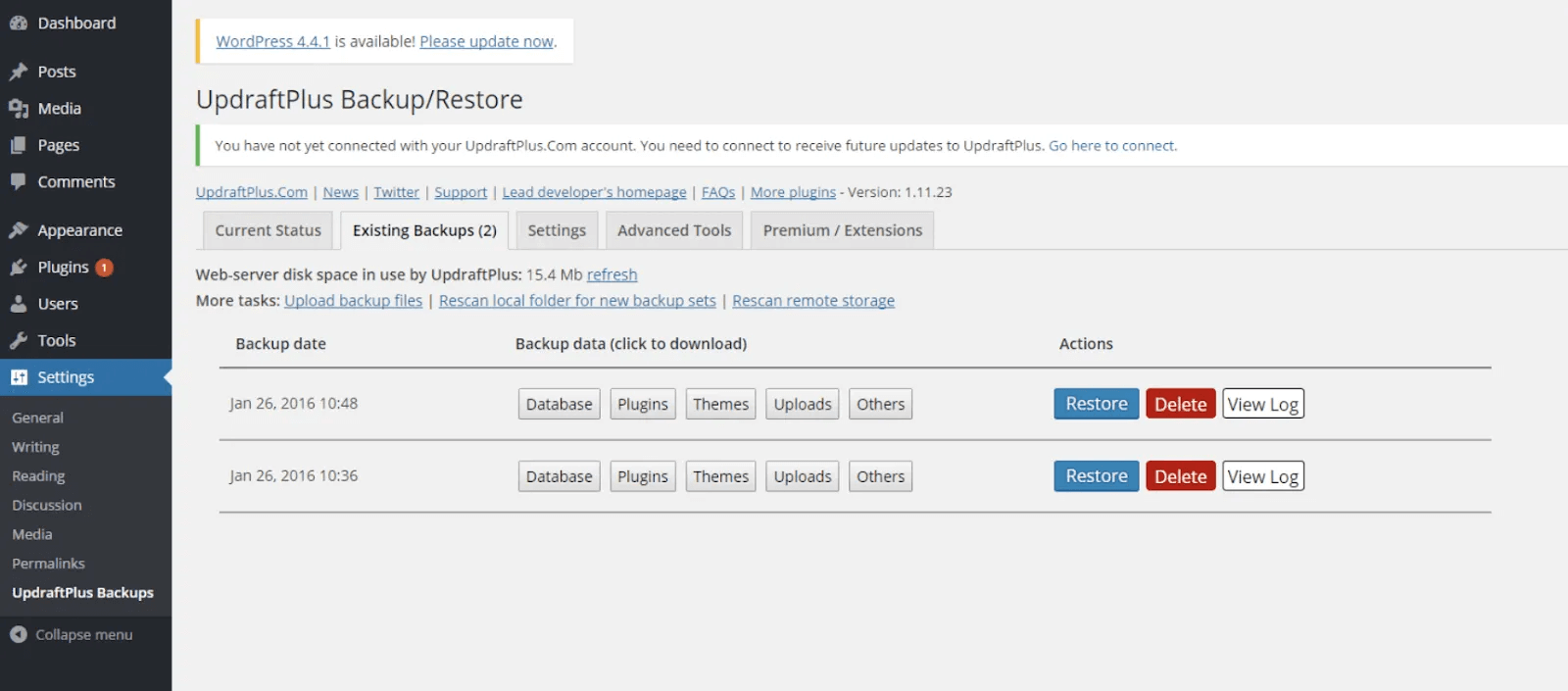
For general backing up, we recommend using UpdraftPlus, a free program to back up your entire site and its critical files.
Follow the link above, download and install the plugin, and “UpdraftPlus” should appear on your dashboard sidebar under “Settings”:
From the UpdraftPlus screen, you can choose when you’d like to back up and where to.
Select “Current Status” and “Backup Now.” The plugin then backs up your site in full.
Step 4: Download and examine your backup files
We recommend downloading an offline backup copy to your drive as an extra precaution. Head to “Existing Backups,” and select what you want to download.
Again, only do this if you can be certain malware hasn’t corrupted your files.
Click “Download to your computer,” choose the saving location, and start the process.
You can also back up your site manually through FTP. However, this process can be complex and time-consuming. We highly recommend you contact an expert, such as a StateWP dev.
Head to your save location and check the downloads. You should see important files such as:
- .htaccess (which you can only see through an FTP client)
- A wp-config.php file (containing configuration and login data)
- An SQL file (your WordPress database)
- A wp-content folder (which contains all your uploads, plugins, and themes files)
Plugins like UpdraftPlus should download all the core files you need to back up safely. However, if you’re concerned, look at WordPress’s list of core files to check you’re covered.
It’s also worth examining your core files for any signs of foul play. Strange code, such as “base64_decode,” “eval,” and “gzinflate” indicate malware’s presence.
In addition, you should ideally check your database tables for signs of malware by logging into cPanel (e.g., through your web host). Specifically, signs of malicious code in your database typically appear in “wp_posts” and “wp_options.”
Again, “base64_decode” and “gzinflate” are common signs of database malware. However, there’s also a chance these functions might be harmless – so take caution before deleting them.
Knowing what to look for in core files is pretty tricky. For a thorough and confident cleaning of your files and database, use a security plugin and call a site security expert.
Remember to scan downloaded files (and your computer again) to be safe.
Step 5: Delete all the files in your public_html folder
You can scan and edit your core files individually for signs of foul play. However, it’s a long and technical process.
We recommend deleting your WordPress files completely and starting again from scratch (provided you’re backed up with what you need).
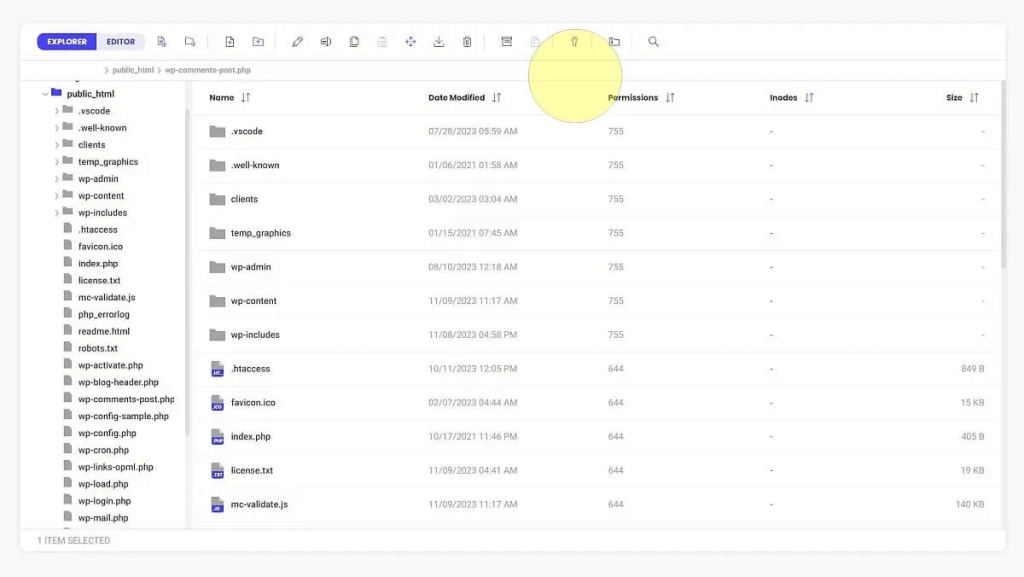
Start by logging into FTP or your File Manager with credentials supplied by your web host. You should see a “root” folder called “public_html.”
Open this folder and delete its contents, but leave the folder wp-content and its subfolder, “uploads,” present but empty. Doing so effectively removes any lingering malware.
Step 6: Reinstall WordPress and reset database credentials
Head to WordPress.org and download the latest version to your preferred drive.
Once downloaded, unzip the file to review its contents. Delete the folder marked wp-content in the unzipped folder and the configuration file, wp-config.php. You now need to upload the remaining files back to public_html.
Head back to your FTP client and your root folder. In Filezilla, you can open your destination folder (i.e., public_html) on the right and your upload folder (the unzipped download) on the left.
Replace the bold sections with your database name, admin username, and password. In most cases, web hosts use “localhost” as the MySQL hostname by default. Save the file.
Here, you can drag files across to public_html or right-click and “Upload.”
Once you’ve uploaded everything from the unzipped folder, check that wp-config uses the right database information for your WordPress site.
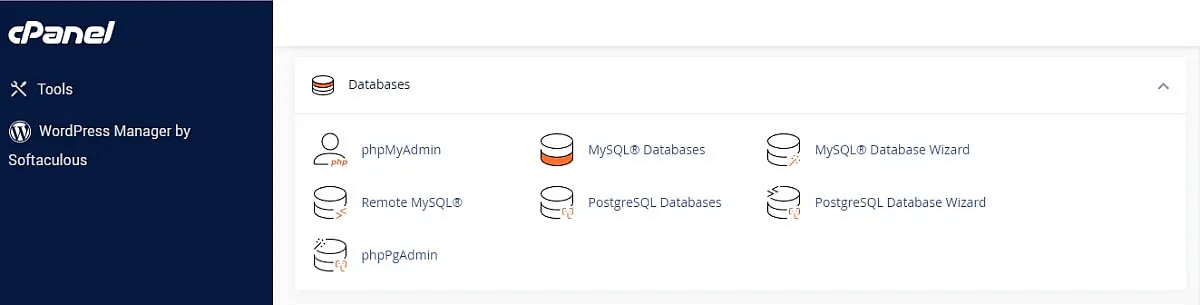
Start by logging into your cPanel account or looking for database information through your web host. To demonstrate, let’s use Bluehost.
Log in, open cPanel, and head down to “Databases,” then “MySQL Databases.”
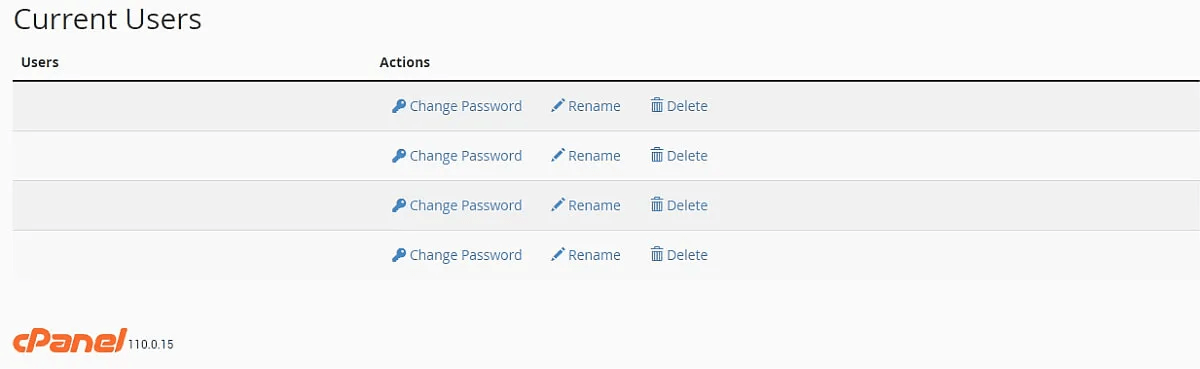
Take note of the database name for your website along with the admin username. You should also change your user accounts’ passwords here by clicking the associated icons and following the instructions.
Check for unexpected usernames in cPanel’s list and remove them, too.
Now, open up wp-config in your root folder in FTP. You should see a series of code lines.
Scroll down, and look for:
| // ** MySQL settings – You can get this info from your web host ** // /** The name of the database for WordPress */ define( ‘DB_NAME’, ‘database_name_here’ ); /** MySQL database username */ define( ‘DB_USER’, ‘username_here’ ); /** MySQL database password */ define( ‘DB_PASSWORD’, ‘password_here’ ); /** MySQL hostname */ define( ‘DB_HOST’, ‘localhost’ ); |
Replace the bold sections with your database name, admin username, and password. In most cases, web hosts use “localhost” as the MySQL hostname by default. Save the file.
Step 7: Reset permalinks
Resetting permalinks ensures WordPress’s structure is complete after recovering from malware. Head to your dashboard, then “Settings,” and then “Permalinks.”
Scroll down the page and click the “Save Changes” button. This restores necessary files in your FTP.
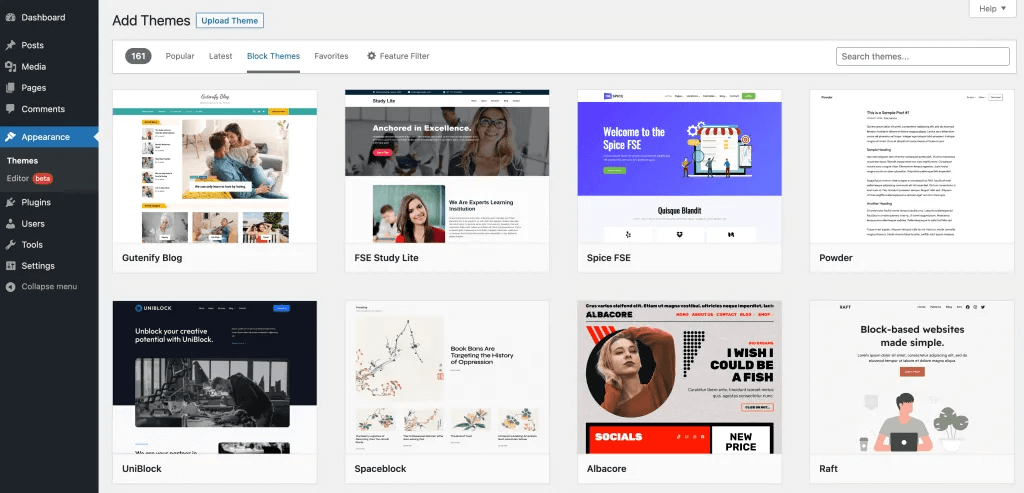
Step 8: Reinstall plugins and themes
Remember, you deleted all your files, so you need to restore your plugins from scratch.
It’s a necessary hassle! Reinstalling your plugins afresh means there’s no risk of your programs carrying sinister code.
Check the plugins downloaded in the “Plugins” backup folder.
Use these to cross-reference. Head to your WordPress dashboard, select “Plugins” from the sidebar, and search for each plugin through the WordPress search engine.
Only download the plugins you use. Too many unnecessary plugins can slow your website’s performance – check out our guide to speeding up WordPress. Remember, “free plugins” doesn’t mean “unlimited plugins.”
To reinstall your theme, head to “Appearance” and “Themes” in your dashboard, and like with your plugins, use the theme browser.
Step 9: Reupload your images
If you want to restore your old images and files, head to your cleaned backup folder or look for the original sources of the media used.
We recommend the latter so you have access to the best-quality media.
After scanning your folders and files, head to FTP and move scanned image files across to your “uploads” folder under “wp-content” in your root.
Step 10: Install and run security plugins
For the future, we recommend installing a WordPress security plugin so you can easily scan and remove most types of malware quickly.
For example, download, install, and activate Wordfence, WordPress’s most popular web application firewall and security scanner.
Then, select your program from your dashboard’s left sidebar. On the plugin page, click “Start New Scan,” and simply wait for the results!
How To Remove Malware With a WordPress Plugin
Removing malware with a WordPress plugin is sometimes the faster and safer way to bounce back from an infection.
However, the efficiency and quality of removal depend on your chosen WordPress malware removal plugin. For this section, we’re using Wordfence.
Take the following steps as a loose guide for any plugin you choose.
1. Scan WordPress for malware
Once you install a malware cleaner for WordPress, you normally see a new icon in the sidebar. Click or tap it, and you typically see a list of options to run scans and set up protection.
Wordfence, for example, lets you choose scan sensitivities and specific areas you’d like it to focus on.
Now, simply click a “start” or “run” scan button from your plugin’s dashboard.
Many malware scanners for WordPress send you email receipts and let you know when scans are complete.
2. Remove malware from your WordPress site
After your plugin completes its scan, a report typically tells you if it found anything suspicious. With Wordfence, you receive a list of files it assumes to be suspicious. This software also lets you erase malware with a click.
Simply work your way through the list of suspected malware and remove anything that looks malicious.
Wordfence also lets you check if there are changes to your files and plugins and lets you repair them again with a single click of a button.
This type of fix is great for low-level threats, but more complex problems, such as those caused by WordPress hacking, require deeper cleaning.
Some malware checkers and plugins can also detect if hackers leave backdoors or if there are malicious entries in your hacked WordPress site’s database tables. Be sure to compare programs!
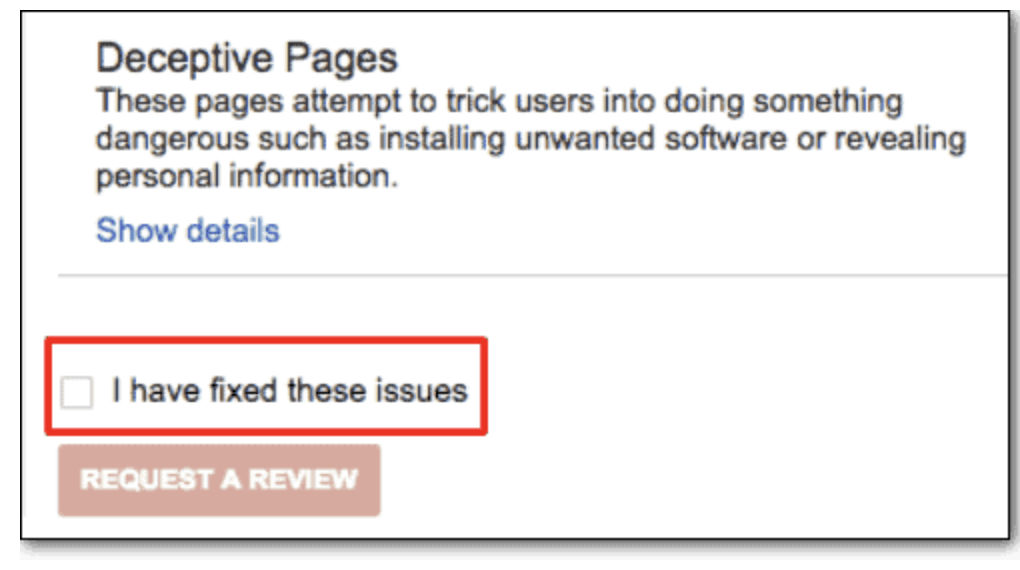
3. Remove malware warnings from Google
Once your site is clean, let Google know that your site is safe to use again (if, say, they put you on the “unsafe” blacklist).
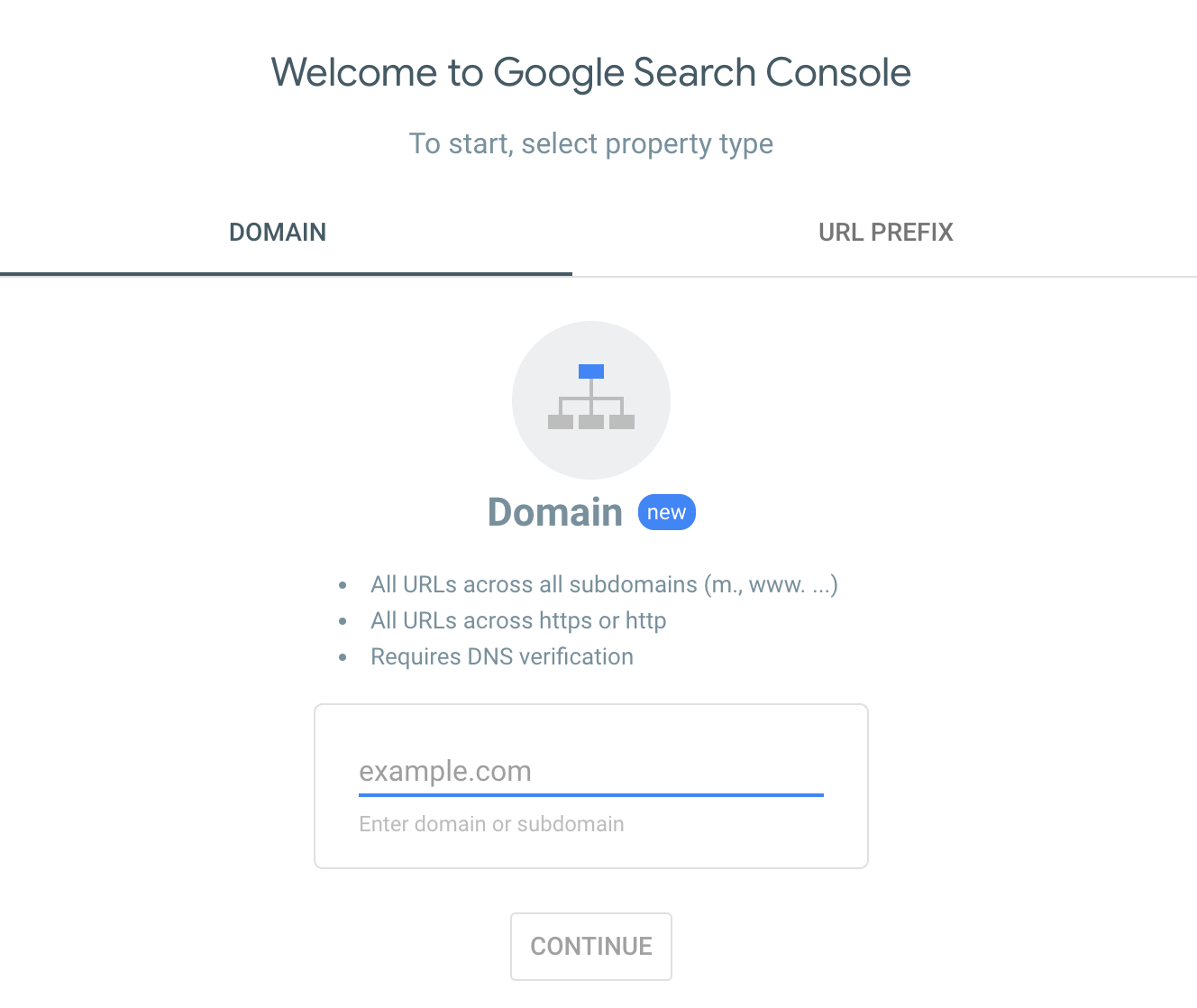
Log into a Google account and head to Google Search Console.
Then, enter your website’s full domain address, and select “Continue.”
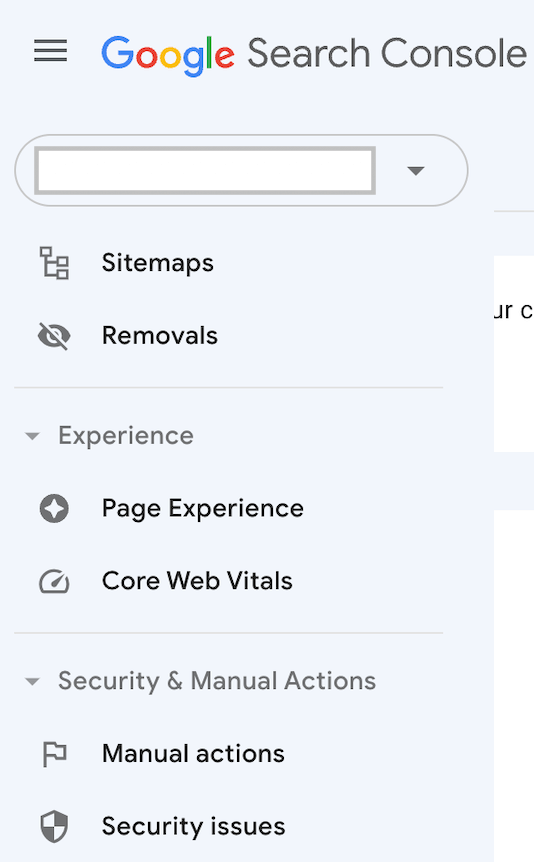
Verify ownership of your site with Google here if needed, and once logged in, select the “hamburger” menu to the left and select “Security & Manual Actions,” then “Security issues.”
When “Deceptive Pages” appears, check the box marked “I have fixed these issues.”
Then, enter details about what you’ve done to remove malware from your site, and submit your request.
Google can take several days to manually read your request, take action, and re-index your site.
If a Google representative returns to advise there are still security vulnerabilities with your website, try clearing your WordPress and browser caches to remove temporary internet files that prevent your site from updating.
Ask an Expert To Remove Malware From Your Site
If you don’t feel confident about removing WordPress malware, or time is pressing, ask for help!
In some cases, your host can help. Log into your host’s dashboard and raise a concern with its team, ask them to back up your site, and potentially reinstall WordPress on your domain (if they offer this service).
Your next option could be to pay for a premium malware removal service. Sucuri and Jetpack are great examples of paid services that erase nasty bugs when they arise.
However, some people feel this approach is a little hands-off and prefer to talk it through with a developer. It’s worth setting up a WordPress maintenance service, for instance, to clean up your site and protect you.
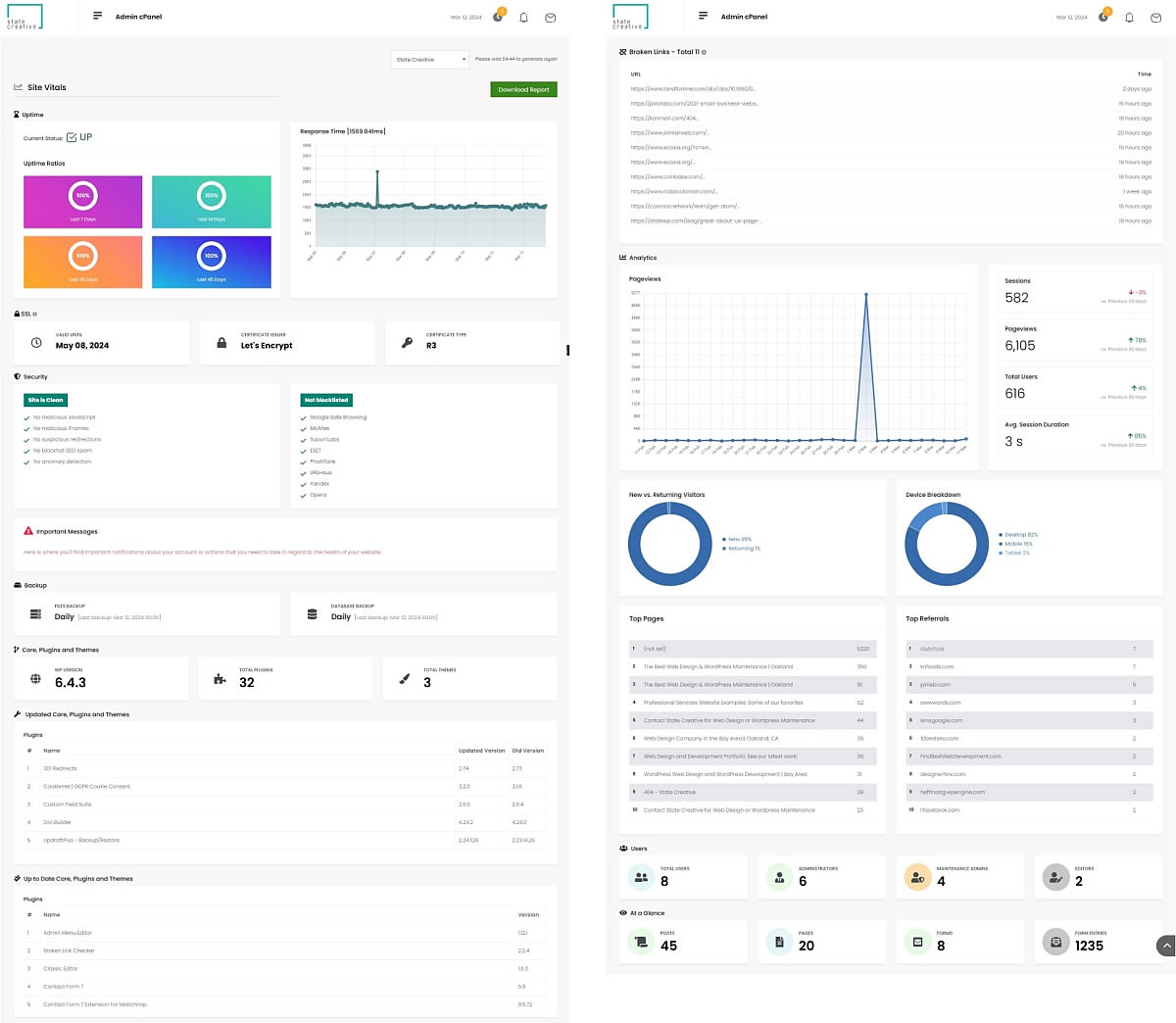
Through Proto, our dedicated WordPress dashboard, you can check your site’s health, uptime, and downtime and get in touch with someone to fix malware problems in a flash.
StateWP’s experts aim to address and fix WordPress issues within a day of receiving requests. Simply head to “Submit a request” from your Proto account and ask our team to weed out malware and restore your site to full health. We can even let Google know you’re safe again.
Contact us to start protecting your site today. We’d love to hear from you.
Symptoms of Having Malware on a WordPress Site
To know if you should start going through all this work or call in the best WordPress malware removal service to help, it’s worth knowing what an infected site looks like.
A red flag many visitors notice is spammy pop-ups and unexpected pages linking to malicious sites. You might also find results for your site on Google showing up with strange characters or meta descriptions.
Hackers using malware also leave traces, such as extra users, post edits, and unfamiliar file names in the hacked WordPress website.
Your host might send you notifications informing you that your site’s showing strange behavior, and they recommend you scan it for malware. You may also notice this yourself in real time if your website starts slowing down unexpectedly, as malware can use more server resources.
Your site users might even tell you they can’t gain access to their accounts or that their antivirus software keeps blocking your site. Your links may even lead to malicious redirects, such as phishing threats.
Lastly, always check your analytics. For example, if there are strange spikes or dips in visitor activity, your site could be funneling traffic elsewhere.
How do WordPress Sites Get Infected With Malware?
Web servers use a handful of rules to determine who gets access to your files. Malware infects WordPress thanks to vulnerabilities in your code, weak passwords, and other security issues.
Let’s explore a few key reasons why you might be infected.
What causes malware on WordPress sites?
| Symptom | In brief |
| Software vulnerabilities | Plugins and themes you haven’t updated are easier for hackers to exploit |
| Weak passwords or security | The easier passwords are to guess, the easier hackers can break into your site and infect you (using brute force attacks) |
| Undetected backdoors | Hackers can leave hidden lines of code in WordPress core files that go undetected until it’s too late |
| Web hosting issues | Less reputable hosts might be easier to exploit (we recommend using private servers) |
| Unsecured communications | Websites not using HTTPS protocols are more vulnerable to infect |
| Unnecessary user privileges | WordPress permissions that are too loose for general users are easy to exploit |
| Old active accounts | Older accounts that haven’t received password updates are easier to break into |
Make WordPress Malware Removal a Cinch
Malware is nasty stuff that can seem quite scary at first. However, WordPress malware removal isn’t often as terrifying as it initially seems.
That said, you still need to take time to remove some files, back up others, install plugins, review folders… it’s a lot.
That’s why it’s always worth having a helping hand on standby at StateWP to check WordPress for malware.
If you spot signs of WordPress malware, just log into Proto, raise a request, and we can fix you up with a clean bill of health.
In the meantime, prevention is better than a cure. Keep on top of your WordPress site’s health with our hassle-free website maintenance checklist.
WordPress Malware Removal FAQs
Let’s take a final look at some common WordPress malware questions.
What is WordPress malware?
How do I run a malware scan on WordPress?
- Installing a WordPress malware detection plugin such as Sucuri or Jetpack
- Opening up the plugin through your WordPress dashboard
- Running a full scan
- Following the instructions to remove the malware
These paid plugins thoroughly scan WordPress sites for common issues and the latest threats.
How do I permanently remove malware from WordPress?
- Using a paid malware scanner plugin
- Paying for a WordPress malware removal service
- Deleting all your files and reinstalling WordPress from scratch
- Contacting an expert developer to do all the hard work for you.
We take you through the best ways to clean your WordPress site and remove malware in our guide above.
How do I prevent malware on WordPress?
Always back up your site and all its data, too! A WordPress malware removal service can offer you further advice.